This morning, The
New York Times published a report detailing how the Bush and Obama
administrations created the cyberweapon known as Stuxnet and used it to disrupt Iran’s uranium enrichment
program.
Much has been written about Stuxnet,
which, as ProPublica
recently reported, remains a threat beyond
Iran. But the Times account, based on interviews with unnamed U.S. and Israeli
officials, is the most extensive account to date of U.S. cyberwarfare capabilities. Here’s
our cheat sheet on what’s new and the fallout:
- Because of Stuxnet’s
complexity, cybersecurity analysts have long
suspected it was a U.S.-Israeli effort. The Times story confirms this for the
first time, disclosing that the project was code-named “Olympic Games.” - Olympic Games began under the Bush
administration, and during development, it was known as “the bug.” - President Obama has repeatedly expressed concern
that if the U.S. acknowledges it is behind Stuxnet, it
would give terrorists and enemy states a justification for their own attacks. - Stuxnet was introduced
into Iran’s enrichment facility at Natanz by an
unwitting Iranian. “It turns out there is always an idiot around who doesn’t
think much about the thumb drive in their hand,” a source told the Times. - To test the bug in secret Department of Energy
labs, the U.S. used aging centrifuges handed over in 2003 by Libyan dictator
Col. Muammar el-Qaddafi, making them into replicas of the nuclear enrichment facilities
Iran used. - The attack on Iran became the first known
instance of the U.S. using computer code to physically damage another country’s
infrastructure. Obama, the Times writes, “was acutely aware that with every
attack he was pushing the United States into new territory, much as his
predecessors had with the first use of atomic weapons in the 1940s, of
intercontinental missiles in the 1950s and of drones in the past decade.” - The
Israeli role in the attack came from a military unit called Unit 8200 that had “technical
expertise that rivaled” the U.S. National Security Agency’s as well as
significant intelligence about Iran’s nuclear facilities. - When a programming error made Stuxnet’s code public in 2010, Obama considered halting Olympic
Games altogether. But in the end, the administration decided to accelerate the
attacks. - It’s unclear who was responsible for the programming
error, but some in the Obama administration blamed the Israelis. The Times
names Vice President Joe Biden:
“Mr. Biden fumed. ‘It’s got to be the Israelis,’ he said. ‘They went too
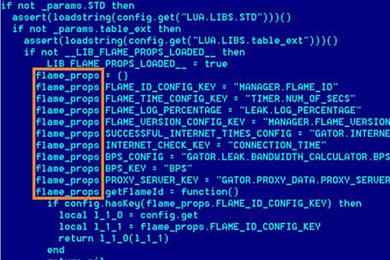
far.’ ” - American officials claim that Flame,
an even more complex piece of computer malware that has also attacked Iranian
infrastructure, is not part of Olympic Games — but they didn’t explicitly
deny it was an American project. - Opinion is divided as to whether Olympic Games
was successful in slowing uranium enrichment in Iran. Administration officials
said they had set the Iranians back 18 months to two years, but other experts
say enrichment
levels quickly recovered and that Iran today has enough fuel for five or
more weapons with additional enrichment.
The Obama administration has long emphasized the importance
of domestic cybersecurity, but recent statements show
an increasing openness about offensive capabilities. Secretary of State Hillary
Clinton acknowledged
last month that government hackers had attacked Al Qaeda propaganda sites
in Yemen, changing information in ads that talked about killing Americans to
show how many Yemenis had died in Al Qaeda attacks.
For years, the Iranians had no idea they were being
attacked, blaming their own workers or faults in their facilities, The Times
said. But because Stuxnet was inadvertently released,
any government— not to mention any hacker with spare time and a malicious
streak — can create their own mutation of the weapon.
As the Times points out, “No country’s infrastructure is more dependent on computer
systems, and thus more vulnerable to attack, than that of the United States.”
Siemens makes specialized industrial controllers that were targeted by the
Olympic Games attacks. As Siemens confirmed to ProPublica, the same hardware and
software holes Stuxnet took advantage of in Iran
exist in thousands of locations in the U.S. and worldwide. The vulnerable equipment
controls everything from natural gas pipelines to refineries and power
transmission lines.
American
cybersecurity experts have long warned that it’s only
a matter of time before someone turns an equally destructive cyberweapon on our own systems. Now that Stuxnet’s origins are clear, the odds of that happening
might be even higher.
Contributing:
Peter Maass of ProPublica